Symptoms
With 1.29.0-wmf.9:
Warning: Empty regular expression in /srv/mediawiki/php-1.29.0-wmf.9/includes/parser/DateFormatter.php on line 200
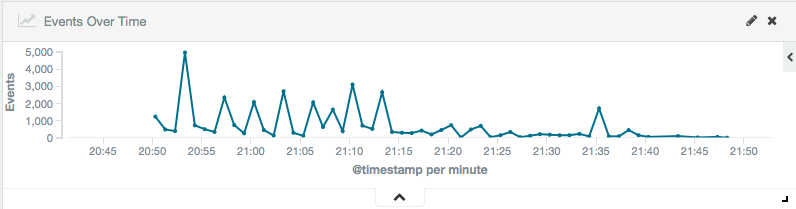
Example of spam after wmf.9 deployments:
- 2017-01-25 20:50 rebuilt wikiversions.php and synchronized wikiversions files: group1 wikis to 1.29.0-wmf.9
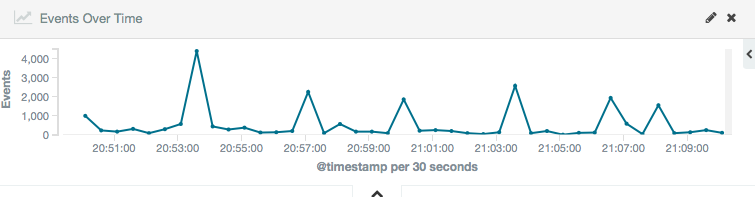
Zoom over 20 minutes highlighting the bursts:
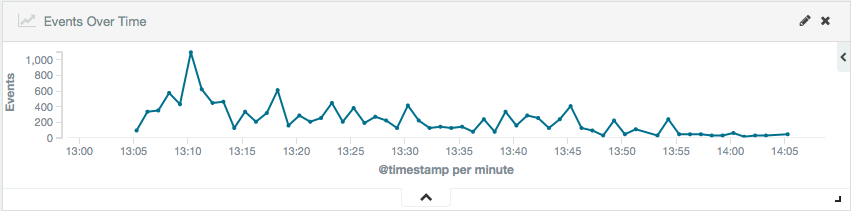
- 2017-01-26 13:01 rebuilt wikiversions.php and synchronized wikiversions files: group1 back to 1.29.0-wmf.9 T156310
In both cases one can see a huge spike after 300?? seconds. And it is vanishing entirely after exactly(?) an hour.
Code
184 $regex = $this->regexes[$i]; 185 186 // Horrible hack 187 if ( !$linked ) { 188 $regex = str_replace( [ '\[\[', '\]\]' ], '', $regex ); 189 } 190 191 if ( $match_whole ) { 192 // Let's hope this works 193 $regex = preg_replace( '!^/!', '/^', $regex ); 194 $regex = str_replace( $this->regexTrail, 195 '$' . $this->regexTrail, $regex ); 196 } 197 198 // Another horrible hack 199 $this->mLinked = $linked; 200 $text = preg_replace_callback( $regex, [ &$this, 'replace' ], $text ); 201 unset( $this->mLinked );
Note the nice comment hoping that will work.