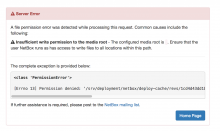
When attempting to upload a photo of the rear of the ulsfo rack 103.02.22, I received the following error:
<class 'PermissionError'> [Errno 13] Permission denied: '/srv/deployment/netbox/deploy-cache/revs/1cd4d43dd1bdf32e81af0318f479890cf23e2ee5/src/netbox/media/image-attachments/rack_33_103.02.22_rear.jpg'
This likely needs some puppetization of the directory permissions, or a review if we want to allow uploads to it at all.