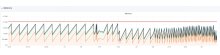
Toolforge Stretch seems to be making more LDAP requests than Toolforge Trusty.
https://phabricator.wikimedia.org/T217280#5008363
Email announcement about Toolforge Trusty deprecation (Feb 7): https://lists.wikimedia.org/pipermail/cloud/2019-February/000533.html
And LDAP restarts: