This issue was first observed for Safari during QA (see below), and we decided to circumvent it by removing Safari user agents from analysis.
Now that the A/B test has launched, we have an additional method to check this: At the beginning of a pageview, the page issues instrumentation (from T191532) is supposed to send a pageLoaded event to both the PageIssues and ReadingDepth schemas. Because ReadingDepth depends on (in particular) support for sendBeacon and the Page Visibility API, we expect the ReadingDepth event to be missing for some browsers or browser versions, in particular Safari as discussed earlier. However, it looks like many other browsers apart from Safari are missing ReadingDepth events too ("only_pi" >> 0% in the table below). In particular, Chrome Mobile iOS, Android (stock browser) and (desktop) Chrome seem worth a closer look.
pageLoaded events logged in the PageIssues or the ReadingDepth schema as part of the page issues A/B test:
| browser | both | only_pi | only_rd | all_pageloads |
|---|---|---|---|---|
| Chrome Mobile | 96.24 | 3.01 | 0.75 | 27759714 |
| Mobile Safari | 78.54 | 21.36 | 0.1 | 22231489 |
| Samsung Internet | 89.68 | 9.38 | 0.94 | rEMFR27519159ecbd |
| Chrome Mobile WebView | 97.71 | 0.88 | 1.41 | 2646714 |
| Chrome | 80.21 | 18.7 | 1.09 | 1928052 |
| Mobile Safari UI/WKWebView | 35.26 | 64.63 | 0.11 | 786079 |
| Android | 4.86 | 95.04 | 0.09 | 474722 |
| UC Browser | 85.91 | 11.89 | 2.21 | 459774 |
| Chrome Mobile iOS | 37.86 | 62.01 | 0.12 | 420661 |
| Firefox Mobile | 96.58 | 1.31 | 2.11 | 390622 |
| Yandex Browser | 87.03 | 11.93 | 1.04 | 273847 |
| Opera Mobile | 95.49 | 3.35 | 1.15 | 267045 |
| Amazon Silk | 98.39 | 0.3 | 1.31 | 169278 |
| YandexSearch | 93.09 | 5.76 | 1.15 | 119939 |
| Edge Mobile | 94.25 | 5.31 | 0.44 | 49999 |
| 90.97 | 8.63 | 0.4 | 48057 | |
| Baiduspider-render | 96.74 | 0.86 | 2.41 | 46165 |
| NetFront NX | 0.0 | 100.0 | 0.0 | 39353 |
| Opera | 92.17 | 6.47 | 1.36 | 25821 |
| Firefox iOS | 53.83 | 46.05 | 0.12 | 21739 |
| Puffin | 61.81 | 36.73 | 1.47 | 19311 |
| BingPreview | 0.04 | 99.96 | 0.0 | 16452 |
| Firefox | 99.27 | 0.49 | 0.24 | 15882 |
| Opera Mini | 0.0 | 100.0 | 0.0 | 11722 |
| BlackBerry WebKit | 0.02 | 99.98 | 0.0 | 10913 |
| QQ Browser Mobile | 80.51 | 15.51 | 3.99 | 10783 |
| Sleipnir | 27.0 | 72.97 | 0.02 | 9258 |
| Crosswalk | 97.49 | 0.69 | 1.82 | 8723 |
| Edge | 97.5 | 2.02 | 0.48 | 7366 |
| Safari | 64.86 | 34.44 | 0.7 | 7251 |
| IE | 1.9 | 98.1 | 0.0 | 3428 |
| IE Mobile | 0.75 | 99.22 | 0.03 | 3208 |
| 89.53 | 9.36 | 1.11 | 2244 | |
| Opera Coast | 0.0 | 100.0 | 0.0 | 2215 |
| Apache-HttpClient | 0.0 | 100.0 | 0.0 | 1064 |
(Data from October 1-7. Browsers with less than 1000 pageviews in this sample removed for readability)
Query:
SET hive.mapred.mode=nonstrict; SELECT browser, ROUND(100*SUM(IF((pipageToken IS NOT NULL) AND (rdpageToken IS NOT NULL),1,0))/SUM(1),2) AS both, ROUND(100*SUM(IF((pipageToken IS NOT NULL) AND (rdpageToken IS NULL),1,0))/SUM(1),2) AS only_pi, ROUND(100*SUM(IF((pipageToken IS NULL) AND (rdpageToken IS NOT NULL),1,0))/SUM(1),2) AS only_rd, SUM(1) AS all_pageloads FROM ( SELECT IF(pi.pageToken IS NOT NULL, pi.browser, rd.browser) AS browser, pi.pageToken AS pipageToken, rd.pageToken AS rdpageToken FROM ( SELECT useragent.browser_family AS browser, event.pageToken AS pageToken FROM event.pageissues WHERE year = 2018 AND month = 10 AND day <=7 AND event.action = 'pageLoaded') AS pi FULL OUTER JOIN ( SELECT useragent.browser_family AS browser, event.pageToken AS pageToken FROM event.readingdepth WHERE year = 2018 AND month = 10 AND day <=7 AND event.action = 'pageLoaded' AND ( event.page_issues_a_sample OR event.page_issues_b_sample )) AS rd ON pi.pageToken = rd.PageToken) AS alltokens GROUP BY browser ORDER BY all_pageloads DESC;
Initial bug report from QA:
In T191532#4575809 @Ryasmeen noticed that it's possible for PageIssues events to be sent without ReadingDepth
Background
ReadingDepth events are only set if sendBeacon is available.
If sendBeacon is not available, PageIssues events can still be sent (using the fallback method)
Developer notes
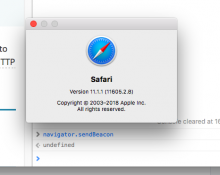
Strangely @Jdlrobson can replicate this in Safari 11.1.1 (which is strange because according to release notes and Caniuse it should support sendBeacon)
On the other hand, we see lots of other Safari 11.1.x clients sending ReadingDepth events (T204143#4578937).
While it is not clear how this is possible, it is technically possible given the current state of the code.
We should investigate possible causes and clarify the implications for the reliability of the ReadingDepth data.
AC:
- @Tbayer to write up outcomes of this investigation and takeaways for data analysis
--> T204143#4895679 and https://meta.wikimedia.org/wiki/Schema_talk:ReadingDepth