In T296847#7745018, @daniel wrote:We had an RFC open about this for a couple of years, which has some analysis and discussion of legitimate use cases and UX for opt-in: T208188: RFC: Partial opt-out method for Content security policy
- Queries
- All Stories
- Search
- Advanced Search
- Transactions
- Transaction Logs
Feed Advanced Search
Advanced Search
Advanced Search
Mar 4 2022
Mar 4 2022
My current plan for rollout is as follows:
- Informal feedback round (in progress)
- Update policy based on feedback.
- New more formal feedback round from WMF staff e.g. please respond by X date
- Update policy based on feedback.
- A formal round of feedback from the community.
- We'll update the interface to provide a notice on pages where JS can be added that links to the policy:
<div class="mw-message-box mw-message-box-notice">All code written here is expected to <a href="#">adhere to the gadget policy</a>.</div>
Feb 16 2022
Feb 16 2022
Following T262493#7584789 I've begun drafting a policy and collating feedback on the talk page:
https://www.mediawiki.org/wiki/User:Jdlrobson/Extension:Gadget/PolicyPerhaps we could combine efforts here?
sguebo_WMF moved T296847: Third-party resources policy from Backlog to In Progress on the Privacy Engineering board.
Feb 15 2022
Feb 15 2022
sguebo_WMF added a comment to T290493: Cross Origin Resource Sharing Misconfiguration | Lead to sensitive information. in "diff.wikimedia.org".
As noted above, WordPress-powered websites such as Diff are used by the Foundation for public-facing initiatives. For instance, blog posts published on Diff feature names of their authors, and in most cases their titles within the organization. Although, the REST API allows people to retrieve the list of user accounts of the website, it generates list of already-public users, in JSON format that'll need to be parsed/processed. Therefore, the API is not disclosing any information that was not already private, nor is it increasing the visibility of information that was already public by making it easier to retrieve.
Dec 8 2021
Dec 8 2021
sguebo_WMF moved T292594: It is possible to construct a list of all globally suppressed users from In Progress to Completed on the Privacy Engineering board.
Dec 6 2021
Dec 6 2021
sguebo_WMF moved T296847: Third-party resources policy from Incoming to Backlog on the Privacy Engineering board.
Dec 2 2021
Dec 2 2021
Dec 1 2021
Dec 1 2021
Oct 29 2021
Oct 29 2021
sguebo_WMF moved T293583: [mwcli] reporting on usage from In Progress to Completed on the Privacy Engineering board.
Hey @Addshore, on the behalf of Security-Team, I reviewed the privacy risks inherent to the proposed usage reporting feature for mwcli. I’ll share my conclusions below.
Oct 26 2021
Oct 26 2021
sguebo_WMF added a comment to T284944: Increased visibility in wiki-replicas for volunteers fighting vandals.
@sguebo_WMF Is this data visible on the wikis?
sguebo_WMF moved T293583: [mwcli] reporting on usage from Backlog to In Progress on the Privacy Engineering board.
For example after a user has gone through a whole setup and played around with the environment a bit we might get something like this (at the highest detail level planned) from the next time the mwcli attempts to send data back.
- 4x docker mediawiki create
- 2x docker mysql create
- 2x docker mediawiki install --dbtype=mysql --dbname=default
- 2x docker mediawiki install --dbtype=sqlite1 --dbname=CUSTOM
- 22x docker mediawiki exec
- 4x codesearch search --output=ack
- 1x codesearch search --output=table
Oct 25 2021
Oct 25 2021
sguebo_WMF awarded Blog Post: How we deploy code a Orange Medal token.
sguebo_WMF updated subscribers of T293811: Clarify whether CUs should share non-public information with external services.
Hey @Addshore -- thanks for bringing that to the Privacy Engineering team's attention. My understanding is that the metric tool would work as below:
sguebo_WMF moved T293583: [mwcli] reporting on usage from Incoming to Backlog on the Privacy Engineering board.
Oct 21 2021
Oct 21 2021
sguebo_WMF moved T292594: It is possible to construct a list of all globally suppressed users from Backlog to In Progress on the Privacy Engineering board.
sguebo_WMF added a comment to T292594: It is possible to construct a list of all globally suppressed users.
localuser: source: - localuser - globaluser view: > select lu_wiki, lu_name, lu_attached_timestamp, lu_attached_method, lu_local_id, lu_global_id where: lu_global_id = gu_id AND gu_hidden=''
Oct 20 2021
Oct 20 2021
sguebo_WMF added a comment to T293811: Clarify whether CUs should share non-public information with external services.
Noted, thanks for the additional context @GeneralNotability. The description was updated accordingly.
sguebo_WMF updated the task description for T293811: Clarify whether CUs should share non-public information with external services.
Oct 19 2021
Oct 19 2021
sguebo_WMF updated subscribers of T292594: It is possible to construct a list of all globally suppressed users.
sguebo_WMF updated subscribers of T293811: Clarify whether CUs should share non-public information with external services.
Hey @GeneralNotability and @Urbanecm. As mentioned earlier, your question will be brought to WMF-Legal's attention. Feel free to rename it or adjust the description if I missed some aspects.
Oct 18 2021
Oct 18 2021
sguebo_WMF moved T292594: It is possible to construct a list of all globally suppressed users from Incoming to Backlog on the Privacy Engineering board.
Oct 8 2021
Oct 8 2021
sguebo_WMF added a comment to T65598: Privacy issues with Gadget-GoogleTrans.js (calls out to google APIs).
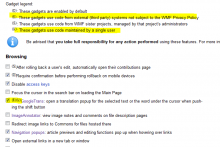
Something more robust would be needed if this is to become any sort of wikimedia, or WMF-wide standard. A longer-term fix would be to integrate such indications in to the software, but development on Gadgets 2.0 has been stalled for a LONG time.
That being said, I don't think "PRIVACY" is very useful there alone - from a UX perspective that seems confusing, did you notice there is already a lengthy hover text on the "E"xternal indicator? It looks like this:
Also keep in mind, there are actually much larger risks then "privacy" when loading third party scripts, such as account hijacking - surreptitious action making, etc.
Oct 1 2021
Oct 1 2021
Sep 20 2021
Sep 20 2021
sguebo_WMF added a comment to T291094: Add "Samuel (WMF)" account to Security Team group in gitlab.wikimedia.org.
Thanks for handling that, @thcipriani
Sep 17 2021
Sep 17 2021
sguebo_WMF added a comment to T289952: Request: expose database tables of the Translate extension to users in replicas on Toolforge (Wikidata, or all Wikis).
On the behalf of Security-Team, I reviewed the privacy risks that exposing Translation extension’s tables in replicas may bring about. I’ll share my conclusions below.
sguebo_WMF added a comment to T289952: Request: expose database tables of the Translate extension to users in replicas on Toolforge (Wikidata, or all Wikis).
In T289952#7359224, @sguebo_WMF wrote:Hey @Nikerabbit and thanks for providing some background on these tables.
You mentioned that translate_messageindex should not be exposed because it contains some internal tracking information. I pulled up an excerpt from that table but I think I would need some help in understanding where you see an issue.
wikiadmin@10.64.16.207(wikidatawiki)> select * from translate_messageindex limit 1\G *************************** 1. row *************************** tmi_key: <redacted integer>:help:About_data/1 tmi_value: page-Help:About data|agg-HelpCould you please explain to me why you think this index information is concerning?
That may help me better grasp any security or privacy risk inherent to this specific table.
Sep 16 2021
Sep 16 2021
sguebo_WMF moved T291094: Add "Samuel (WMF)" account to Security Team group in gitlab.wikimedia.org from Incoming to Waiting on the Privacy Engineering board.
sguebo_WMF added a comment to T289952: Request: expose database tables of the Translate extension to users in replicas on Toolforge (Wikidata, or all Wikis).
Hey @Nikerabbit and thanks for providing some background on these tables.
Sep 15 2021
Sep 15 2021
sguebo_WMF updated subscribers of T65598: Privacy issues with Gadget-GoogleTrans.js (calls out to google APIs).
Sep 13 2021
Sep 13 2021
Sep 10 2021
Sep 10 2021
Sep 9 2021
Sep 9 2021
sguebo_WMF added a comment to T195578: Deploy access to performance_schema/sys for the administrative mediawiki account (mediawiki deployers).
Thank you for your answer. I have now wrapped the privacy review and would like to share the conclusion. The analysis focused on the sys database of db2083 server, which as of writing, contains 88 tables, encompassing performance statistics.
sguebo_WMF added a comment to T195578: Deploy access to performance_schema/sys for the administrative mediawiki account (mediawiki deployers).
In T195578#7335760, @Marostegui wrote:@sguebo_WMF thanks a lot for starting to take a look into this.
sys schema has lots of view (this is the documentation about them: https://dev.mysql.com/doc/refman/5.7/en/sys-schema-views.html) to be honest, I am not fully sure which ones could leak private information.If this is helpful in trying to identify what can be potentially private, this is an output of one row per table, in case something rings a bell and you want to explore the table further:
Thanks for pasting the output of sys’ tables, @Marostegui. That’s really helpful. As I am wrapping up my analysis, I’d like to ask a quick question just to make sure that I understand things correctly. The host_summary table seems to contain IP addresses in the 10.192.** range. Judging by the range, my understanding is that these IPs are from Wikimedia load balancer and not from the end user. Is my understanding accurate?
Sep 3 2021
Sep 3 2021
In T279952#7329494, @mforns wrote:@sguebo_WMF & @EYener, we discussed this task and will go ahead and implement this feature.
However, as it is something not trivial, we won't be able to do it this quarter.
We're aiming to tackle it next quarter.
sguebo_WMF added a comment to T195578: Deploy access to performance_schema/sys for the administrative mediawiki account (mediawiki deployers).
In T195578#7321195, @LSobanski wrote:That would be great. There is no real rush, I've just been reviewing blocked tasks that have been silent for a while.
sguebo_WMF added a comment to T290099: Create a "delete me" maintenance script for special user/data deletion requests.
In T290099#7322617, @RhinosF1 wrote:Note: Miraheze has the RemovePII mediawiki extension for compliance with RTBF. There might be bits you can steal.
Interesting - https://github.com/miraheze/RemovePII does indeed look like it could maybe get us part of the way there.
Aug 30 2021
Aug 30 2021
sguebo_WMF awarded T279952: event.WikipediaPortal referer modification a Like token.
Aug 27 2021
Aug 27 2021
Hey @mforns, that confusion is totally understandable so not worries at all. The good thing is that I have now updated my title in Phabricator.
Aug 24 2021
Aug 24 2021
sguebo_WMF moved T279952: event.WikipediaPortal referer modification from Backlog to Completed on the Privacy Engineering board.
In T279952#7034307, @mforns wrote:A couple comments.
- The other day, talking with the team, we thought we Analytics could take this task, as sanitizing a full URL by applying a mask, could be useful to other data sets. This is something we could do, I created a task for it: T281144.
- On the other hand, I thought that, even if we purge the URL and only leave the hostname, that could still hold privacy sensitive information, that could indicate user's preferences or interests or specific situation. I think we should ask the Security/Privacy team about this. Pinging @JFishback_WMF, what do you think?
Aug 16 2021
Aug 16 2021
sguebo_WMF added a comment to T284941: [S] Add note explaining that EXIF geolocation metadata may be uploaded with Commons images.
In T284941#7267325, @CBogen wrote:Hi @sguebo_WMF! Do you have suggestions about what language we should use to inform users that information about them will be collected via the EXIF data and made public? Or do you suggest we reach out to legal?
Aug 6 2021
Aug 6 2021
sguebo_WMF moved T284944: Increased visibility in wiki-replicas for volunteers fighting vandals from In Progress to Completed on the Privacy Engineering board.
sguebo_WMF added a parent task for T284944: Increased visibility in wiki-replicas for volunteers fighting vandals: Unknown Object (Task).
sguebo_WMF moved T284948: Raw IPs of logged-out users disclosed in wiki-replicas from In Progress to Watching on the Privacy Engineering board.
sguebo_WMF added a parent task for T284943: User genders publicly disclosed in wiki-replicas global_preferences and user_properties tables: Unknown Object (Task).
sguebo_WMF added a parent task for T284941: [S] Add note explaining that EXIF geolocation metadata may be uploaded with Commons images: Unknown Object (Task).
sguebo_WMF added a parent task for T284944: Increased visibility in wiki-replicas for volunteers fighting vandals: Unknown Object (Task).
sguebo_WMF added a parent task for T284948: Raw IPs of logged-out users disclosed in wiki-replicas: Unknown Object (Task).
sguebo_WMF updated the task description for T284948: Raw IPs of logged-out users disclosed in wiki-replicas.
I used replica databases to evaluate wide anon-only range blocks applied to certain ISP(s), and for those tasks, having raw IP of (logged out) users is certainly beneficial.
sguebo_WMF updated subscribers of T284941: [S] Add note explaining that EXIF geolocation metadata may be uploaded with Commons images.
Hi @Seddon, I am adding this task to the Structured Data board and pinging you here, following the above discussion about some privacy concerns related to the Upload Wizard.
Jul 29 2021
Jul 29 2021
Jul 27 2021
Jul 27 2021
sguebo_WMF added a comment to T284943: User genders publicly disclosed in wiki-replicas global_preferences and user_properties tables.
I agree that the privacy harm is considerably lowered by the fact that users are made aware that their gender information will be made public if they choose to disclose it. Since it is my understanding that we’re comfortable moving on with that low level of privacy risk, I don't see any issue with declining the ticket.
Jun 25 2021
Jun 25 2021
sguebo_WMF added a comment to T284943: User genders publicly disclosed in wiki-replicas global_preferences and user_properties tables.
In T284943#7156513, @bd808 wrote:@sguebo_WMF Is this a modification of the approval given in T150679: Some Labs DB user_properties view fields are sensitive to expose that preference?
sguebo_WMF added a comment to T284941: [S] Add note explaining that EXIF geolocation metadata may be uploaded with Commons images.
For context, the privacy engineering audit regarding the wiki-replicas is part of a body of work that is being done internally by the Security team. But I concur that a parent public ticket would have made sense too. I’ll keep that in mind moving forward.
Jun 14 2021
Jun 14 2021
May 12 2021
May 12 2021
sguebo_WMF added a comment to T259421: WordPress blogs load (unused) Twemoji.js which uses third-party service.
I had the chance to sync directly with @Varnent who's in charge of those platforms, and I surfaced the solutions proposed above. So far, applying the CSP change at the Nginx server level on WordPress VIP does not seem to be an option. Instead, disabling Twemoji.js through a WordPress plugin would be the applicable solution. The Security-Team is supportive of this approach, which was suggested earlier in this thread and has already been used on the techblog (Cf: 4447d8f).
May 4 2021
May 4 2021
sguebo_WMF updated the task description for T279140: Prototyping a vulnerability management dashboard.
Apr 30 2021
Apr 30 2021
sguebo_WMF added a comment to T65598: Privacy issues with Gadget-GoogleTrans.js (calls out to google APIs).
Thank you again for the mockup. I had the chance to surface it to WMF-Legal and I'd like to ask something. Is it possible to make the privacy indicator a bit more obvious? A few ideas to consider would be either giving the indicator a distinct color, or making its size larger, or putting them in bold, or using "(Privacy)" instead of the "(E)" indicator. Kindly let me know what's feasible or not.
Apr 26 2021
Apr 26 2021
sguebo_WMF added a comment to T275754: Fix (non-default) gadgets loading executable JavaScript from third-party URLs.
In T275754#7031267, @Waihorace wrote:Thanks for the ping. I have added a sentence to reflect the concern on the gadget description for zhwikinews where I am a sysop.
Indeed, @Xiplus , do you find it feasible if we move your script to the wiki so that the concern could be eliminated?
sguebo_WMF updated the task description for T275754: Fix (non-default) gadgets loading executable JavaScript from third-party URLs.
Apr 23 2021
Apr 23 2021
sguebo_WMF added a comment to T275754: Fix (non-default) gadgets loading executable JavaScript from third-party URLs.
The Foundation’s Privacy Policy mentions the commitment of “never selling [user] information or sharing it with third parties for marketing purposes” and “[...]only sharing [user ]information in limited circumstances, such as to improve the Wikimedia Sites, to comply with the law, or to protect you and others.” In principle, gadgets that share user information with third parties do so in violation of this policy. However, it is worth noting that some of these scripts are used by thousands of contributors. Therefore, I think there should be a short-term and a long-term approach to tackling this issue.
sguebo_WMF added a comment to T65598: Privacy issues with Gadget-GoogleTrans.js (calls out to google APIs).
In T65598#7027012, @Xaosflux wrote:
Hey @Xaosflux ,
Thanks for producing the mockup. I'll run this by WMF-Legal and revert back to you.
Apr 19 2021
Apr 19 2021
sguebo_WMF added a comment to T275754: Fix (non-default) gadgets loading executable JavaScript from third-party URLs.
I would be grateful if you clarify what you are requesting/ expecting. Are you suggesting that those gadgets be taken down or that their authors be required to draft an on-wiki heads-up, for instance on the widget's talk page? Or is it totally something else you're asking for?
Apr 15 2021
Apr 15 2021
sguebo_WMF added a comment to T259421: WordPress blogs load (unused) Twemoji.js which uses third-party service.
In T259421#6374107, @sbassett wrote:In T259421#6373857, @Krinkle wrote:Since the WordPress blogs have none of the MW legacy, I suppose it'd make sense to set the CSP rules at the server-level for the blogs, not from within PHP.
I'm not sure if we have access to nginx config settings at Auttomatic, but that would be the best approach, sure. I was more implying that we could copy the current Wikimedia prod CSP as a starting point and tighten it as appropriate for the various WP sites referenced within this task.
Apr 9 2021
Apr 9 2021
Originally I was interested in having the risk rating field being added to New Task. However, while looking at the tickets your referenced, I could see that the Security Type Advanced form (73) already has the Security rating field, although it seems to be locked at the moment.
Apr 8 2021
Apr 8 2021
sbassett awarded T279690: Enable risk rating field in Phabricator's task form a Like token.
sguebo_WMF updated the task description for T279140: Prototyping a vulnerability management dashboard.
sguebo_WMF renamed T279690: Enable risk rating field in Phabricator's task form from Enable risk rating field in Phabricator's New task form to Enable risk rating field in Phabricator's task form.
Apr 6 2021
Apr 6 2021
sguebo_WMF updated the task description for T279140: Prototyping a vulnerability management dashboard.
I completed a prototype with basic filtering options. For now, one can filter by project (tag), year when the ticket was created, and severity. The code base is available at https://github.com/samuelguebo/vm-dashboard. It's public for now since there are no credentials or sensitive data there but I'm glad to make it private if there are any objections.
Apr 2 2021
Apr 2 2021
Thanks @Reedy, I intend to use the Phabricator's Python library since it's pretty straightforward.
I guess I can grab the token with you once you've gotten the chance to create it.
Content licensed under Creative Commons Attribution-ShareAlike (CC BY-SA) 4.0 unless otherwise noted; code licensed under GNU General Public License (GPL) 2.0 or later and other open source licenses. By using this site, you agree to the Terms of Use, Privacy Policy, and Code of Conduct. · Wikimedia Foundation · Privacy Policy · Code of Conduct · Terms of Use · Disclaimer · CC-BY-SA · GPL · Credits